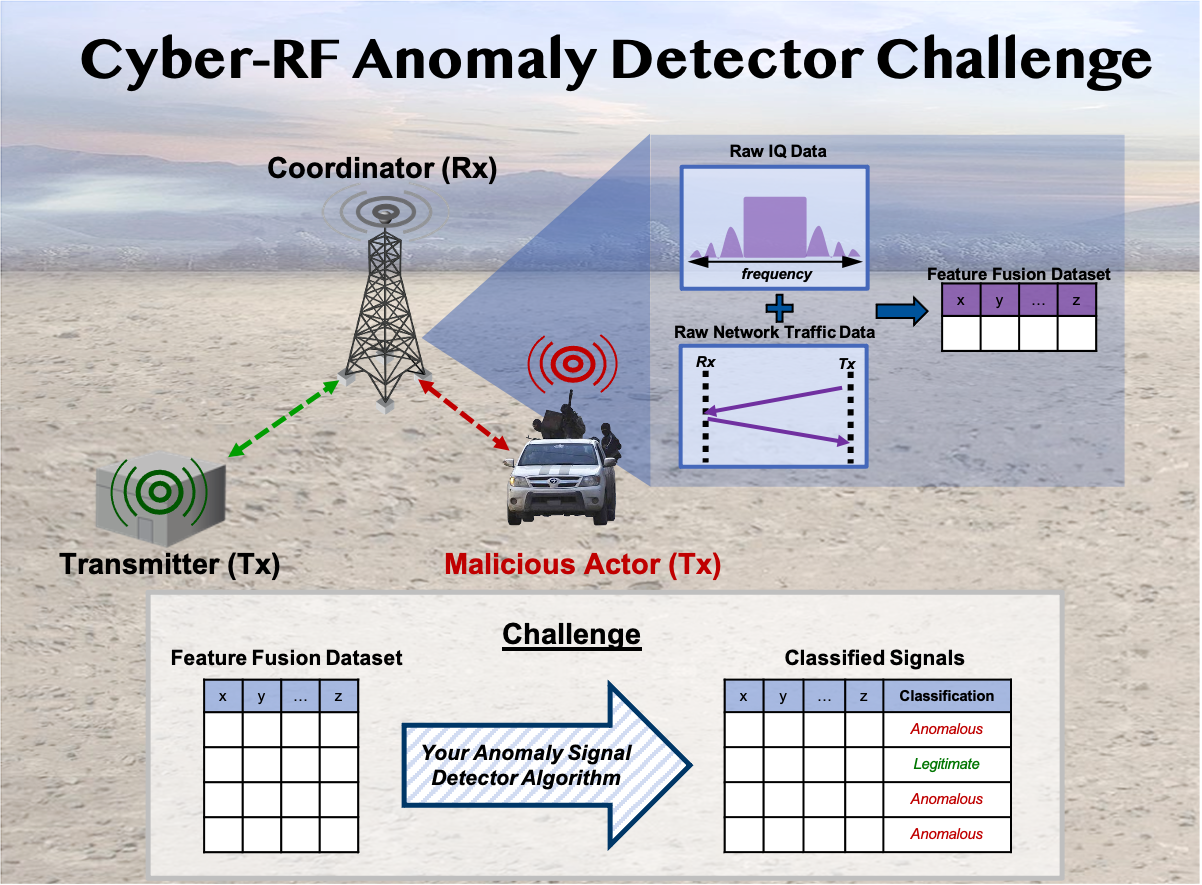
Cyber-RF Anomaly Detector Challenge
Wireless networks provide mission-critical infrastructure for public safety, national security, and military communications. The value of wireless networks in these applications is derived from their accessibility and availability. However, this popularity makes them vulnerable to cyber-attacks such as jamming, spoofing, and eavesdropping. To help address this research problem, we are releasing the Cyber-RF anomaly detector challenge. For this challenge, participants will be tasked with classifying anomalous Zigbee transmissions at the physical layer. Zigbee was chosen as a starting point as it is a popular communication protocol used to create personal area networks with small, low-power digital radios.
During the data captures, both the IQ data and network traffic data were recorded. The legitimate Zigbee data shows characteristics of a valid Zigbee signal, while for the anomalous Zigbee two cyber-attacks (a replay attack and a rogue transmitter use case) were simulated in addition to the legitimate signal. The replay attack simulates a malicious actor who records a signal from the transmitter and duplicates the transmissions to the coordinator at a later time, while the rogue transmitter scenario includes a malicious actor that creates and transmits new packets that are sent to the coordinator.
The provided dataset contains features extracted from IQ (e.g., Kurtosis, and entropy of the Amplitude and Phase) and network traffic data (e.g., packet size and the duration of the network flows). To assess the performance of the participant’s solutions, it is encouraged to compute metrics such as the Accuracy, Recall, and False Positive Rate (FPR) from a confusion matrix. By submitting their solutions, participants are helping the USAF with the development of new capabilities to improve how to monitor, classify, and detect RF signals in the spectrum.
Challenge Details
Click here for details on the challenge setup
Dataset
Click here for this challenge dataset
Dataset Description
Click here for the dataset description of this challenge